Plank Security
Security as a Service
The ultimate security platform that offers Security as a Service (SECaaS).
Benefits
Peace of mind
Pre accesses management
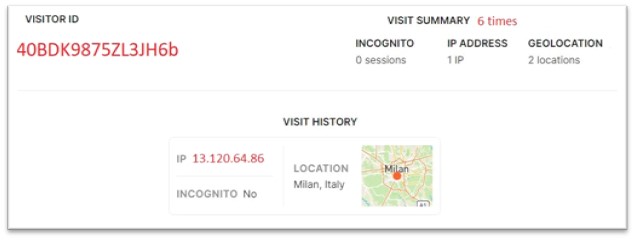
Plank associate to every user an unique identification code through a digital fingerprint algorithm. Plank will not enable users to access until the preaccess process is completed through user confirmation of the SMS or email they will receive upon first access. At that point, they will be assigned a unique fingerprint that will track every activity desired by the admins.
Activities monitoring
Pre-access active management and log monitoring
Users' devices and attempts overview
Revoke or enable accesses to users or devices
Rules & Alerts
Set access time limits
Apply accesses restrictions on specific IP addresses or userst
Apply downloads rules to specific users, groups, or IP addresses
Receive notifications via email or SMS for alerts
Ability to grant or restrict accesses to Plank sections to any user you desire
How it works
Fingerprint Check
All web traffic is encrypted via HTTPS and TLS 1.2
Information is transferred server-side and transmitted securely to our servers using a server-to-server API so information is never exposed in the browser
Advanced machine learning combines browser fingerprints, IP/URL analysis, device analysis and, with a complex algorithm, creates a unique identification code
Section Preview
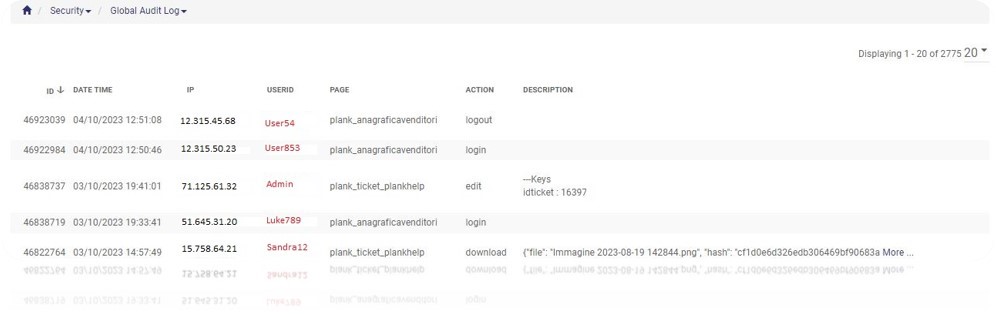
Global Audit Log
Activities
Monitoring
Ability to grant access to this section to any user you desire;
Monitor login, logout, edit and downloads of every user;
Filter: Plank allows you to apply filters to every search, whether it's for a user, page, or specific date and time.
Security
Benefits
Associate current users with previous instances of fraud, even when they attempt to conceal their identity;
If someone gains access to the CRM using an unauthorized device or credentials, we have a response in place.
DOCUMENT AND CREDENTIALS STORAGE
VAULT
Enterprise level security with SHA 512 encryptions. Safe password management with banking grade audit logs. Protect your data with the best firewall and realtime backups routine. Encrypt everything you want with your key word. All file are encrypted in an irreversible way. Feel safe that only the ones who know the key and have the access to the specific data can decrypt it.
DATA SECURITY
Backup Policies
Data Centers:
Our management software benefits from robust backup policies implemented across our data centers located in Ohio, London, and Frankfurt. These strategically positioned centers ensure the security of mirrored data across multiple servers.
Backup Frequency